Free Download Pass4sure and Lead2pass CWNP PW0-204 Exam Question with PDF & VCE (31-40)
QUESTION 31
Which of the following security protocols is supported by Wi-Fi Protected Access (WPA)?
A. CCMP
B. LEAP
C. TKIP
D. PEAP
Answer: C
QUESTION 32
What WLAN security function can be performed by the illustrated software utility? (Choose 3)
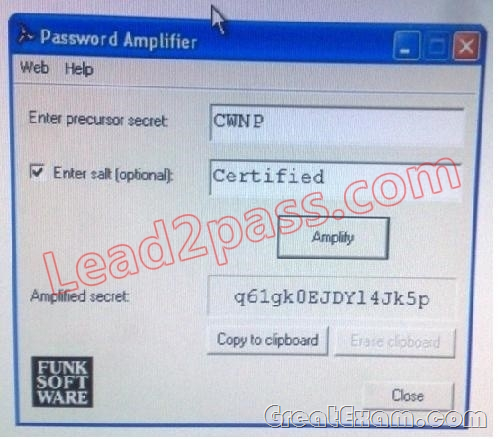
A. Generating PMKs that can be imported into 802.11 RSN systems
B. Generating passphrases for WLAN system secured with WPA2-personal
C. Generating random EAP-TTLS session keys
D. Generating passwords for WLAN infrastructure equipment logins
E. Generating high-entropy EAP-TLS passphrase for client authentication
F. Generating secret keys for RADIUS server and WLAN infrastructure devices
Answer: BDF
QUESTION 33
You work as a Network Administrator for Tech Perfect Inc. The company has a wireless LAN network. The clients present on the network are excluded. You check the error and find the reason that there is no DHCP server. Which of the following devices will you configure as a DHCP server?
A. Access point
B. Controller
C. RADIUS Server
D. Wireless LAN switches
Answer: B
QUESTION 34
The exhibit shows one of the ABC Company’s APs and its associated clients. AP-00:1F:C3is configured with three separate WLAN profile, as follows
Two of the clients stations that are connected via the ABCData SSID are corporate executives. Theses executives are the part of multicast group that is used to share sensitive videos among executive users.
What client stations possess the key that are necessary to decrypt the multicast data packets charring theses sensitive videos?

A. Only the members of executive team that are the part of the multicast group
B. All clients that are associated to AP-00:IF:C3 using the ABCData SSID
C. All clients that are associated to AP:00:IF:C:3 with shared GTK, which includes ABCData and ABC voice
D. All clients that are associated to AP-00:IF:C3 using any SSID
Answer: B
QUESTION 35
A Cisco Unified Wireless Network has an AP that does not rely on the central control device of the network. Which type of AP has this characteristic?
A. Rogue AP
B. LWAPP
C. Lightweight AP
D. Autonomous AP
Answer: D
QUESTION 36
Which of the following wireless security protocols is defined in IEEE 802.11 pre-RSNA security?
A. TKIP
B. WEP
C. EAP
D. CCMP
Answer: B
QUESTION 37
Which of the following security levels are applied on the network to prevent unauthorized access?
Each correct answer represents a complete solution. Choose all that apply.
A. Access control lists
B. Authentication
C. Authorization
D. MAC filtering
Answer: BC
QUESTION 38
Which of the following are legacy authentication protocols used within the stronger EAP authentication protocols? Each correct answer represents a complete solution. Choose all that apply.
A. MS-CHAP
B. PPTP
C. PAP
D. CHAP
Answer: ACD
QUESTION 39
You are setting up small offices for a major insurance carrier. The company policy states that all wireless configurations must fully implement the 802.11i standard. Based on this requirement, which encryption algorithm should you implement?
A. WEP
B. PKI
C. WPA2
D. WPA
Answer: C
QUESTION 40
Which of the following monitors program activities and modifies malicious activities on a system?
A. RADIUS
B. NIDS
C. HIDS
D. Back door
Answer: C
If you want to pass the CWNP PW0-204 exam sucessfully, recommend to read latest CWNP PW0-204 Dumps full version.
